一、认识traefik
1.1 traefik简介
- 参考链接:https://traefik.cn/
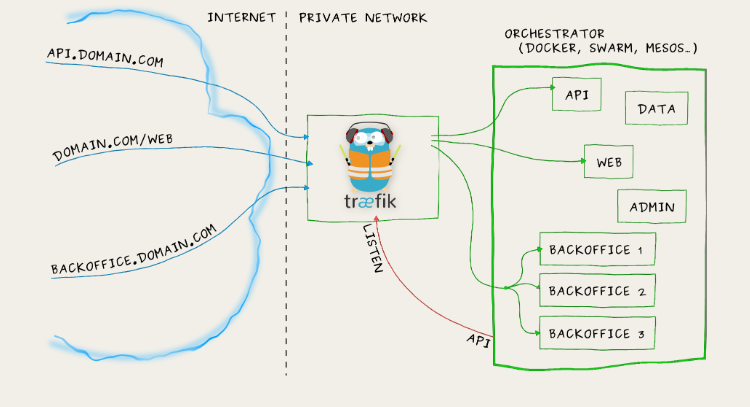
- 是一个为了让部署微服务更加便捷而诞生的现代HTTP反向代理、负载均衡工具
- 它支持多种后台(Docker,Swarm,Kubernetes,Marathon,Mesos,Consul,Etcd,Zookeeper,BoltDB,Rest API,file…)来自动化、动态的应用它的配置文件设置。
1.2 traefix 特性
- 非常快
- 无需安装依赖,通过Go语言编写的单一可执行文件
- 支持Rest API
- 多种后台支持:Docker,Swarm,Kubernets,Marathon,Mesos,Consul,Etcd 并且还会更多
- 后台监控,可以监听后台变化进而自动化应用新的配置文件设置
- 配置文件热更新,无需重启进程
- 正常结束http连接
- 后端断路器
- 轮询,rebalancer负载均衡
- Rest Metrics
- 支持最小化docker 镜像
- 前后台支持SSL
- 清爽的AngularJS 前端页面
- 支持websocket
- 支持HTTP/2
- 网络错误重试
- 支持Let’s Encrypt (自动更新HTTPS证书)
- 高可用集群模式
1.3 traefik 与 nginx ingress对比
| 对比项 | APISIX ingress | Kubernetes Ingress | NGINX Ingress | Kong Ingress | Traefik | HAproxy | Istio Ingress | Ambassador |
|---|---|---|---|---|---|---|---|---|
| 协议 | http/https, http2, grpc, tcp/udp, tcp+tls, Dubbo | http/https, http2, grpc | http/https, http2, grpc, tcp/udp | http/https, http2, grpc | http/https, http2, grpc, tcp, tcp+tls | http/https, http2, grpc, tcp, tcp+tls | http/https, http2, grpc, tcp, tcp+tls, mongo, mysql, redis | http/https, http2, grpc, tcp, tcp+tls |
| 基础平台 | openresty/tengine | nginx/openresty | nginx/nginx plus | openresty | traefik | haproxy | envoy | envoy |
| 路由匹配 | path, method, host, header, nginx 变量,args 变量,自定义函数 | host, path | host, path | path, method, host, header | host, path, headers, query, path prefix, method | host, path | host, path, method, headers | host, path, method, headers |
| 命名空间支持 | - | 共用或指定命名空间 | - | 指定命名空间 | 共用或指定命名空间 | 共用或指定命名空间 | 共用或指定命名空间 | 共用或指定命名空间 |
| 部署策略 | ab 部署、灰度发布、金丝雀部署 | 金丝雀部署,ab 部署 | - | 金丝雀部署、蓝绿部署 | 金丝雀部署、蓝绿部署 | 蓝绿部署 | 金丝雀部署、蓝绿部署、灰度部署、根据 header 白名单 | 金丝雀部署、蓝绿部署、灰度部署、根据 header 白名单 |
| upstream 探测 | 重试、超时、心跳探测、熔断 | 重试、超时 | 重试、超时、心跳探测 | 心跳探测、熔断 | 重试、超时、心跳探测、熔断 | 探测 url、ip、port | 重试、超时、心跳探测、熔断 | 重试、超时、心跳探测、熔断 |
| 负载均衡算法 | 一致性 hash, WRR | RR, 会话保持,最小连接,一致性 hash, EWMA | RR, 会话保持,最小连接,最短时间,一致性 hash | WRR, 会话保持 | WRR, 动态 RR, 会话保持 | RR, static-RR, 最小连接,源 ip, uri, uri param, uri header, 会话保持 | RR, 会话保持,一致性 hash, maglev 负载均衡 | RR, 会话保持,一致性 hash, maglev 负载均衡 |
| 鉴权方式 | key-auth, OpenID Connect | basic-auth, oauth | - | basic, Key, HMAC, LDAP, Oauth 2.0, PASETO, OpenID Connect | basic, auth-url, external auth | basic-auth, Oauth, Auth TLS | basic, external auth, Oauth, OpenID | basic, external auth, Oauth, OpenID |
| JWT | ✅ | - | ✅ | ✅ | ✅ | ✅ | ✅ | ✅ |
| DDOS 防护能力 | limit-conn, limit-count, limit-req, ip-writelist | limit-conn, limit-count, limit-req, ip-writelist | rate-limit | limit-conn, limit-count, limit-req, ip-writelist, response limit | limit-conn, limit-req, ip-writelist | limit-conn, limit-req, ip-writelist | limit-req, ip-writelist | limit-req, ip-writelist |
| 全链路跟踪 | ✅ | ✅ | - | ✅ | ✅ | ✅ | ✅ | ✅ |
| 协议转换 | grpc, Dubbo | - | - | - | grpc | - | grpc, mongo, mysql, redis | grpc, mongo, mysql, redis |
1.4 traefik核心概念及能力
Traefik 是一个边缘路由器,它会拦截外部请求并根据逻辑规则选择不同的操作方式,这些规则决定着这些请求到底该如何处理。Traefik提供自动发现能力,会实时检测服务,并自动更新路由。
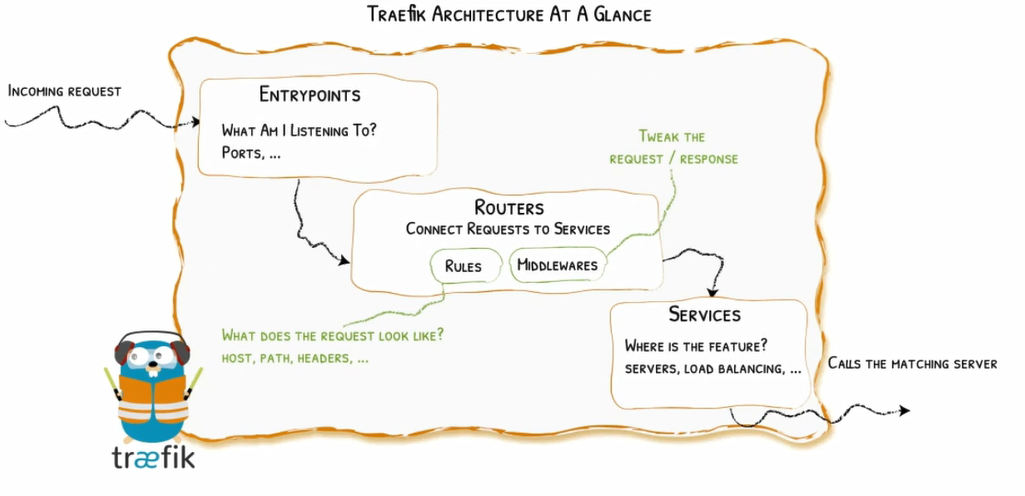
请求首先会连接到entrypoints,然后分析这些请求是否与定义的rules匹配,如果匹配,则会通过一系列middlewares,再到对应的services上。
这就是涉及到以下几个核心的组件:
providers
providers是基础组件,Traefik的配置发现是通过它来实现的,它可以是协调器,容器引擎,云提供商或者键值存储
Entrypoints
Entrypoints 是 Traefik的网络入口,它定义接收请求的接口,以及是否监听TCP或者UDP。
Routers
Routers主要用于分析请求,并将这些请求连接到对应的服务上去,在这个过程中,Routers还可以使用MiddleWares来更新请求,比如在把请求发到服务之前添加一些Headers。
Services
Services 负责配置如何到达最终将处理传入请求的实际服务。
MiddleWares
Middlewares用来修改请求或者根据请求来做出一些判断(authentication,rate limiting,headers,……),中间件被附件到路由上,是一种在请求发送到你的服务之前(或者在服务的响应发送到客户端之前)调试请求的一种方法。
二、traefik 部署
2.1 获取traefik 部署前置资源清单文件
2.1.1 创建CRD资源(官方建议使用Helm安装)
yaml资源
# Install Traefik Resource Definitions:
kubectl apply -f https://raw.githubusercontent.com/traefik/traefik/v3.6/docs/content/reference/dynamic-configuration/kubernetes-crd-definition-v1.yml
# Install RBAC for Traefik:
kubectl apply -f https://raw.githubusercontent.com/traefik/traefik/v3.6/docs/content/reference/dynamic-configuration/kubernetes-crd-rbac.yml
**kubernetes-crd-definition-v1.yml ** 官方默认
**kubernetes-crd-rbac.yml ** 修改namespace
1 | [root@master1 ~]# cat kubernetes-crd-rbac.yml |
- traefik.config
1 | apiVersion: v1 |
- deployment
1 | apiVersion: apps/v1 |
- service
- **localbalancer service ** 之前安装过loadbalancer L2 ip_pool
1 | apiVersion: v1 |
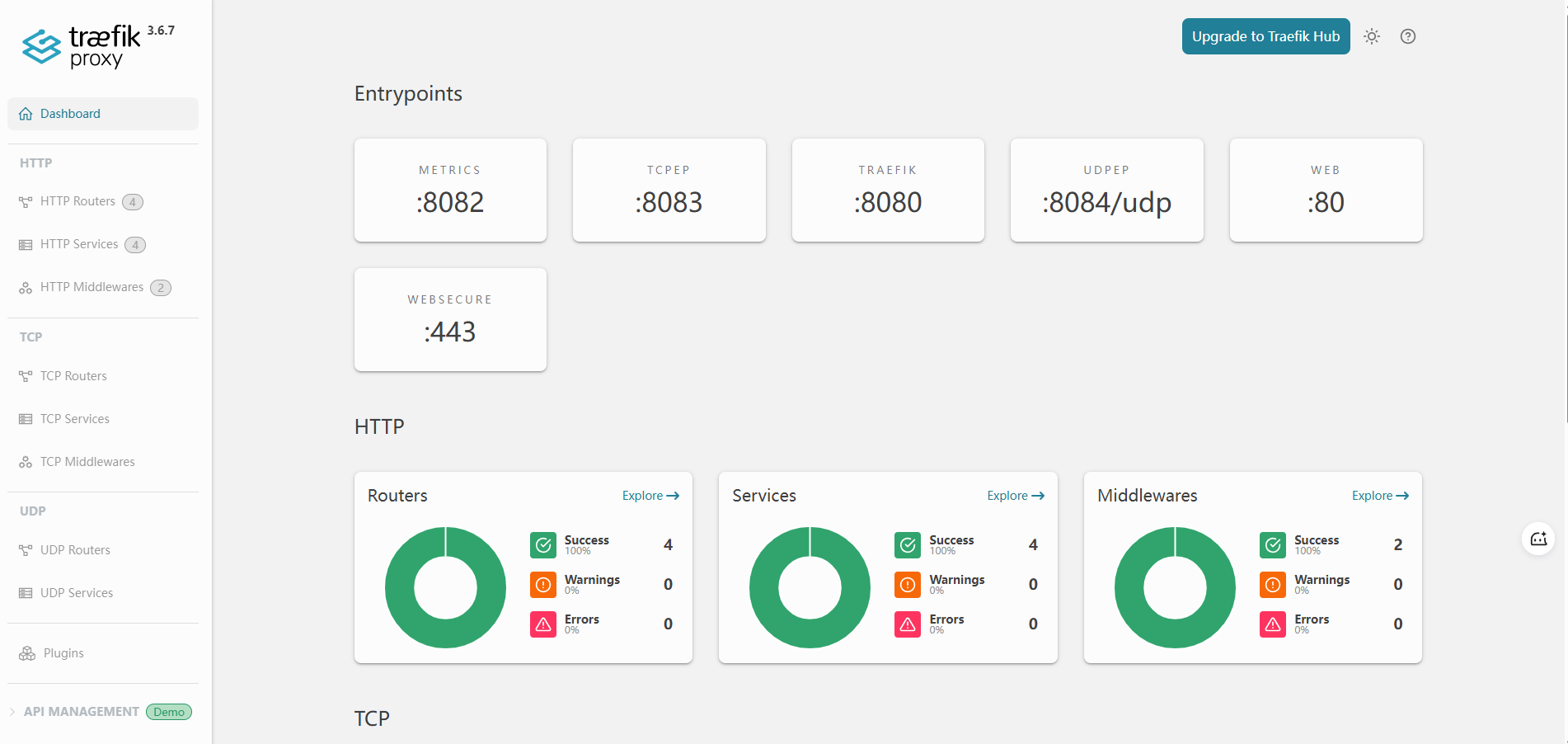
http://192.168.11.20:8080/dashboard/#/
- DaemonSet 部署
1 | [root@master1 traefik]# kubectl label nodes --all traefik=true |
daemonset.yaml
1 | [root@master1 traefik]# cat daemonset.yaml |
1 | 外部流量: 用户 → 节点IP:80/443(hostPort) → Traefik Pod |
cluster svc
1 | [root@master1 traefik]# kubectl get svc -n traefik |
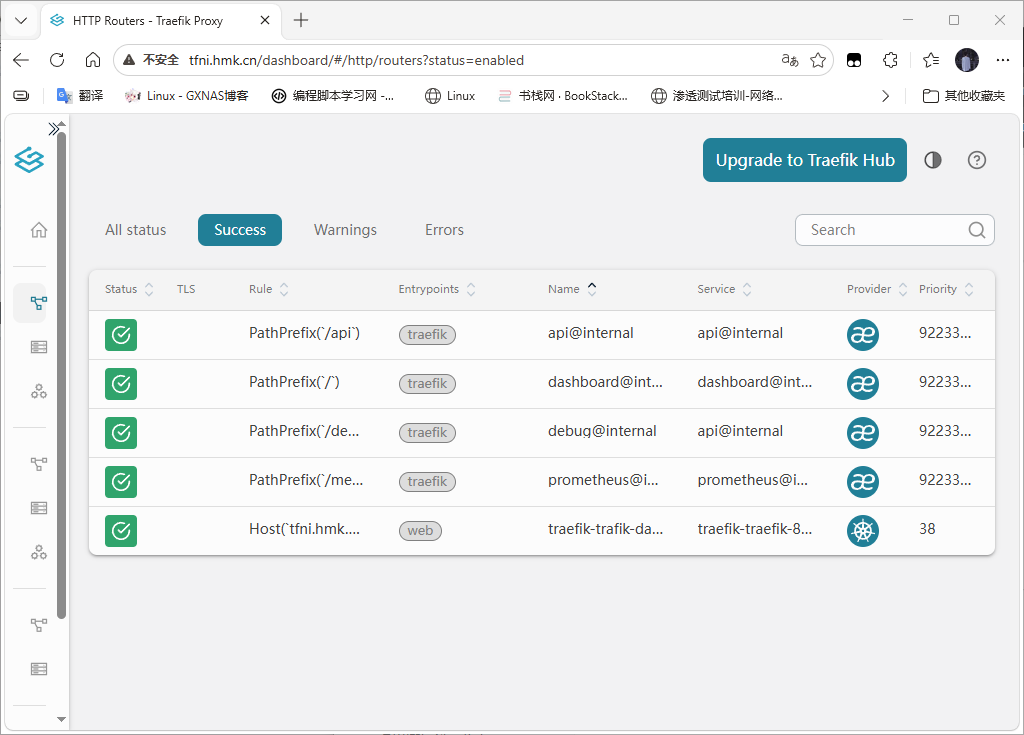
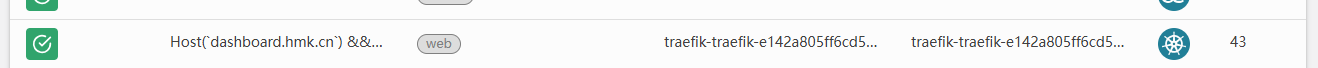
2.2 配置访问traefik Dashboard 路由规则
Traefik应用已经部署完成,但是想让外部访问Kubernetes内部服务,还需要配置路由规则,上面部署Traefik时开启了TraefikDashboard,这是Traefik提供的视图看板,所以,首先配置基于HTTP的Traefik Dashboard 路由规则,使外部能够访问TraefikDashboard。这里使用 IngressRoute方式进行演示。
2.2.1 traefik 创建路由规则方法
- 原生ingress
- CRD Ingress Route
- GateWay API
2.2.1.1 traefik dashboard访问 原生ingress方式
必路由规则 须和对应的service 在一个命名空间
1 | apiVersion: networking.k8s.io/v1 |
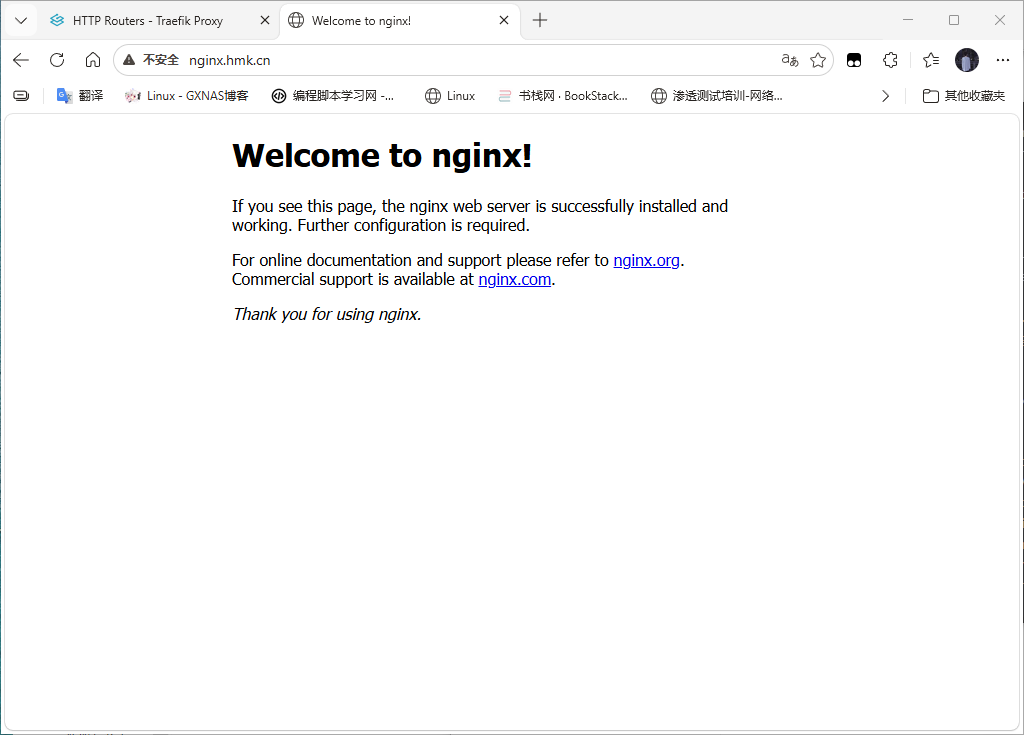
测试 nginx
1 | kubectl run hmknginx --image=registry.cn-hangzhou.aliyuncs.com/hemingkang/nginx:1.20.0 --port=80 |
注解方式deprecated
[root@master1 traefik]# kubectl apply -f traefik-dashboard.yaml
WarninF: annotation “kubernetes.io/ingress.class” is deprecated, please use ‘spec.ingressClassName’ instead
ingress.networking.k8s.io/trafik-dashboard created
修改config 使用edit 或者直接删除 (建议edit)
1 | kubernetesIngress: |
1 | # traefik-ingressclass.yaml |
重建traefik
kubectl rollout restart daemonset traefik -n traefik
1 | apiVersion: networking.k8s.io/v1 |
2.2.1.2 traefik dashboard访问 crd ingressroute方式
1 | [root@master1 traefik]# cat traefik-dashboard-crdingressroute.yaml |
hosts 解析
1 | 192.168.11.5 tfni.hmk.cn |
三、traefik基础应用
客户端 → 宿主机 IP:hostPort → Traefik Pod(直接)→ IngressRoute → 业务 Service → 业务 Pod
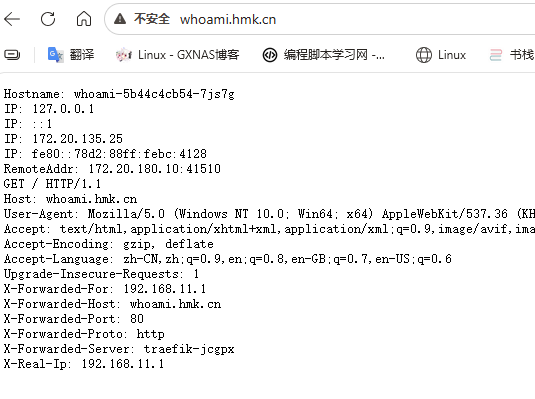
3.1 配置HTTP路由规则
3.1.1 创建应用及服务资源清单文件并应用
1 | [root@master1 traefik-whoami]# cat whoami.yaml |
3.1.2 创建whoami应用ingress route 资源清单文件并应用
1 | [root@master1 traefik-whoami]# cat whoami-ingressroute.yaml |
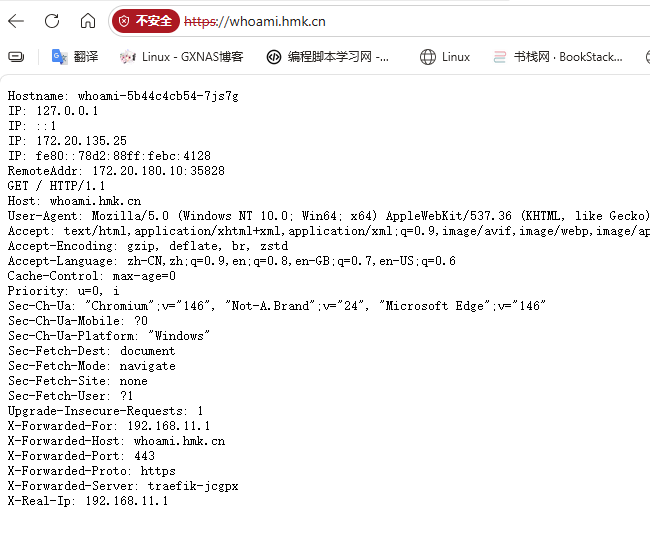
3.2 配置HTTPS路由规则
HTTPS 来访问应用,需要监听websecure 这个入口,通过443端口来访问,需要证书
3.2.1 自签名证书
1 | openssl req -x509 -nodes -days 3650 -newkey rsa:2048 -keyout tsl.key -out tls.crt -subj "/CN=whoami.hmk.cn" |
3.2.2 创建secret
1 | kubectl create secret tls who-tls --cert=tls.crt --key=tls.key |
3.2.3 创建https 应用路由规则
1 | [root@master1 traefik-whoami]# cat whoamissl-ingress.yaml |
3.3 配置TCP路由规则
SNI为服务名称标识,是TSL协议的扩展。因此,只有TLS路由才能使用该规则指定域名。但是,非TLS路由必须使用带有*的规则(每个域)来声明每个非TLS请求都将由路由进行处理。
1 | [root@master1 traefik-whoami]# |
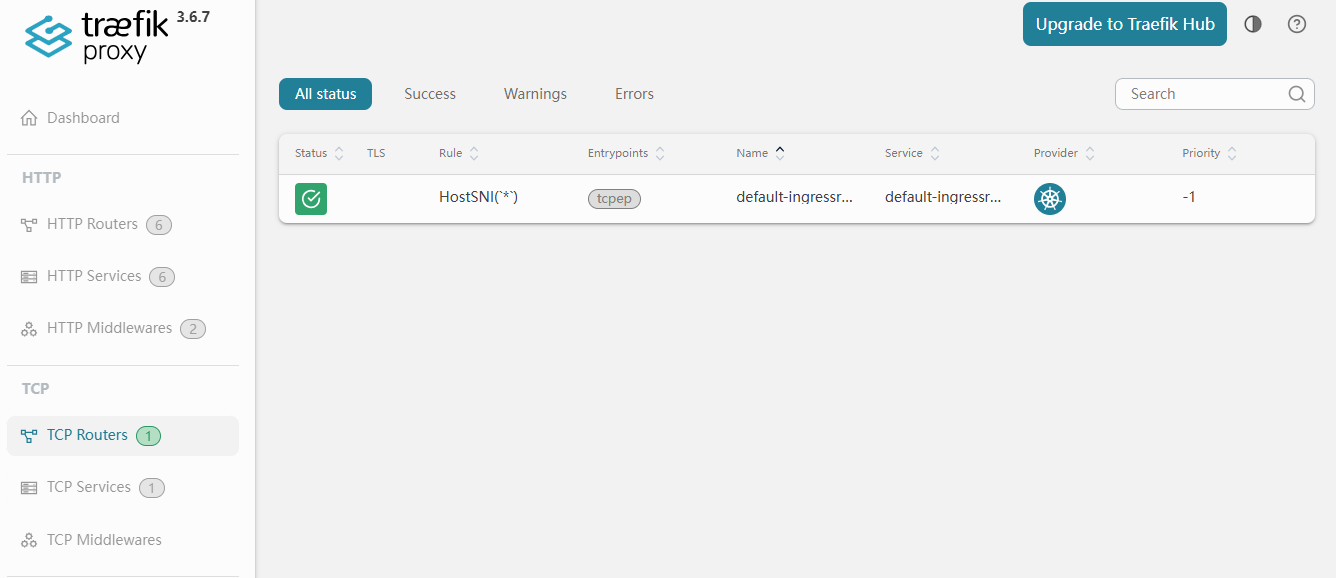
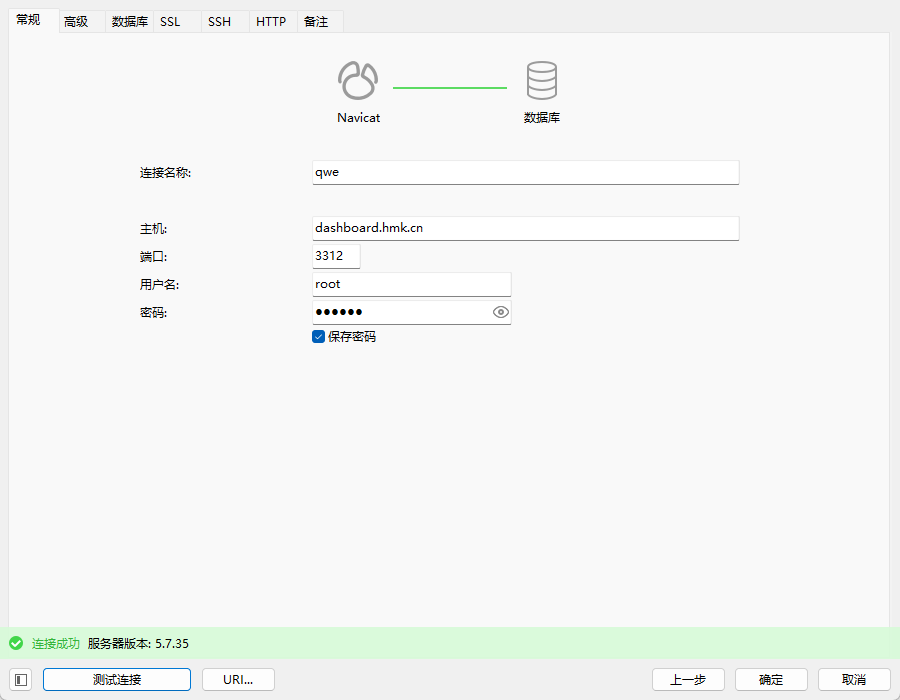
3.3.1 配置MySQL部署 traefik代理
3.3.1.1 修改traefik configmap 增加入口
1 | cat configmap.yaml |
3.3.1.2 部署mysql应用 测试使用deploy
1 | [root@master1 mysql]# cat mysql-deploy.yaml |
3.3.1.3 为mysql应用创建ingressroute
1 | [root@master1 mysql]# cat mysql-ingresstcp.yaml |
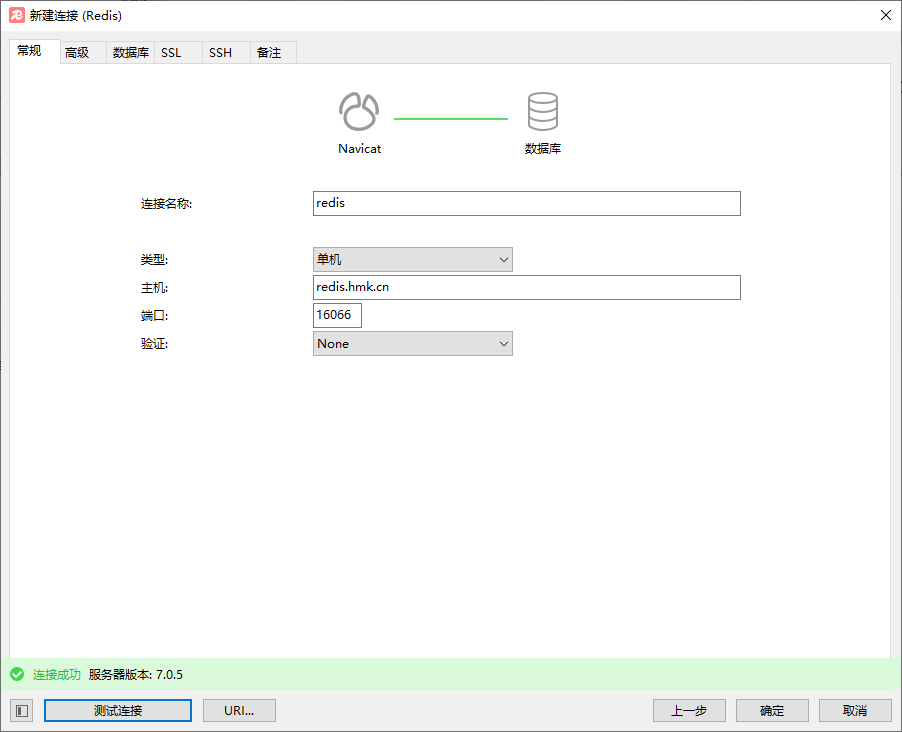
3.3.2 配置redis 部署traefik代理
核心规则
| 配置项 | 必须一致? | 说明 |
|---|---|---|
静态配置 entryPoints |
必须 = containerPort | Traefik 进程监听的端口 |
| containerPort | 必须 = entryPoints | Pod 内容器暴露的端口 |
| hostPort | 可以 ≠ containerPort | 宿主机映射端口,自定义 |
1 | 静态配置 entryPoints:6379 ──┐ |
1 | configmap.yaml |
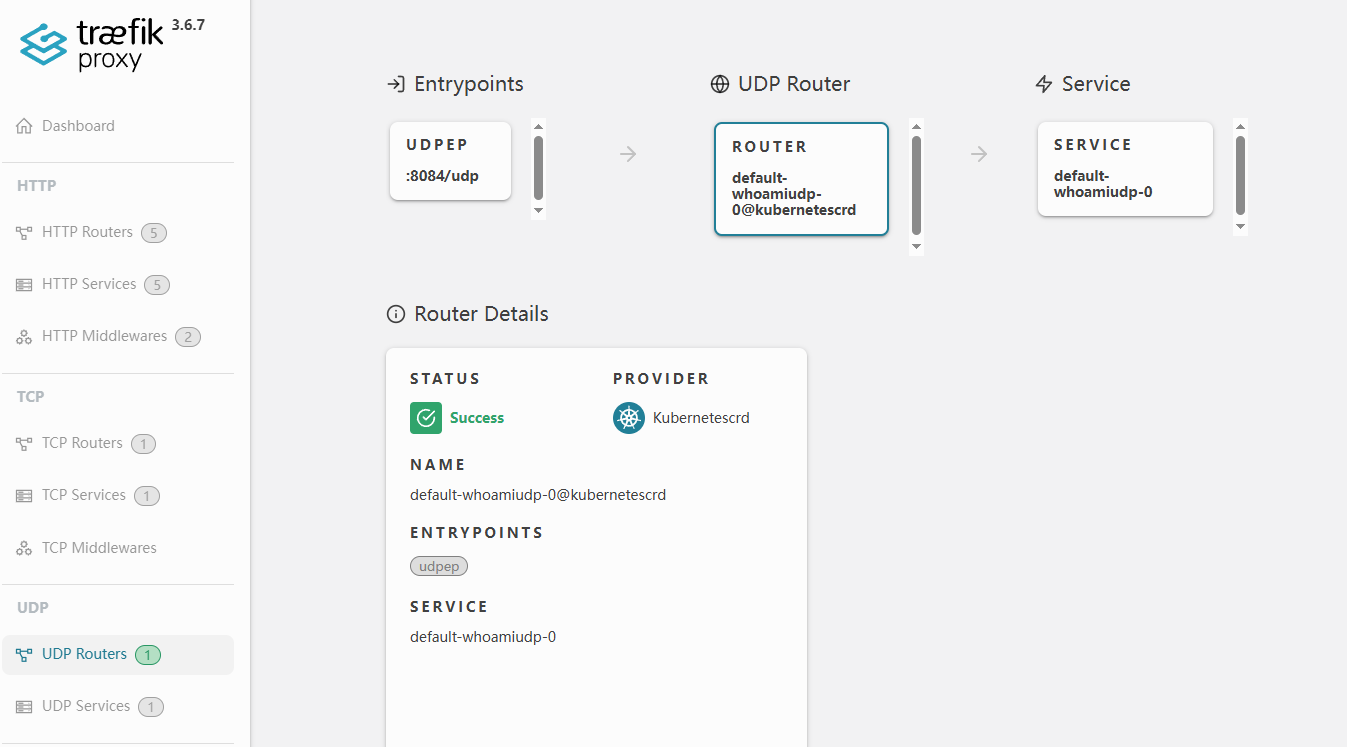
3.4 配置UDP 路由规则
1 | [root@master1 traefik]# kubectl get pods |
1 | [root@master1 traefik]# cat traefik-ingresswhoamitcp.yaml |
1 | [root@master1 traefik]# echo "WHO" | socat - udp4-datagram:192.168.11.8:8084 |
四、traefik中间件 MiddleWare
4.1 traefik中间件介绍MiddleWare
中间件是Traefik2.0中一个非常有特色的功能,我们可以根据自己的各种需求去选择不用的中间件来满足服务,Traefik官方已经内置了许多不同功能的中间件,其中包括修改请求头信息;重定向;身份验证等等,而且中间件还可以通过链式组合的方式来适用各种情况。例如:强制跳转https,去除访问前缀,访问白名单等。
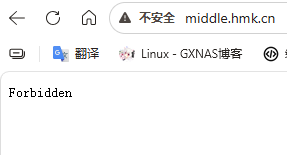
4.2 traefik 中间件应用案例 ipWhiteList
在一些环境中,对某些URL并不希望对外暴露,比如promethus、grafana等,我们就可以通过白名单ip来达到要求。可以使用traefik中的ipwhitelist中间件来完成。
测试清单
1 | [root@master1 middleware]# cat deploy-service.yaml |
ipwhitelist
1 | [root@master1 middleware]# cat middleware-ipwhitelist.yaml |
ingressroute
1 | [root@master1 middleware]# cat middle-ingressroute.yaml |
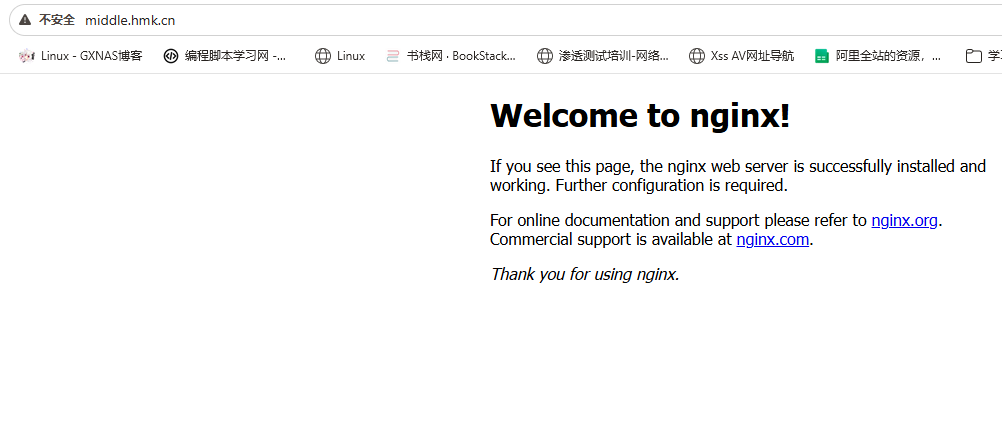
删除宿主机网络192.168.11.0/24
五、traefik高级应用
在实际的生产环境,除了线上业务之外,还有更复杂的使用要求。
在开始traefik的高级用法之前,还需要了解一个TraefikService,通过TraefikService 注册到CRD来实现复杂的请求设置
1 | TraefikService 目前能用于以下功能 |
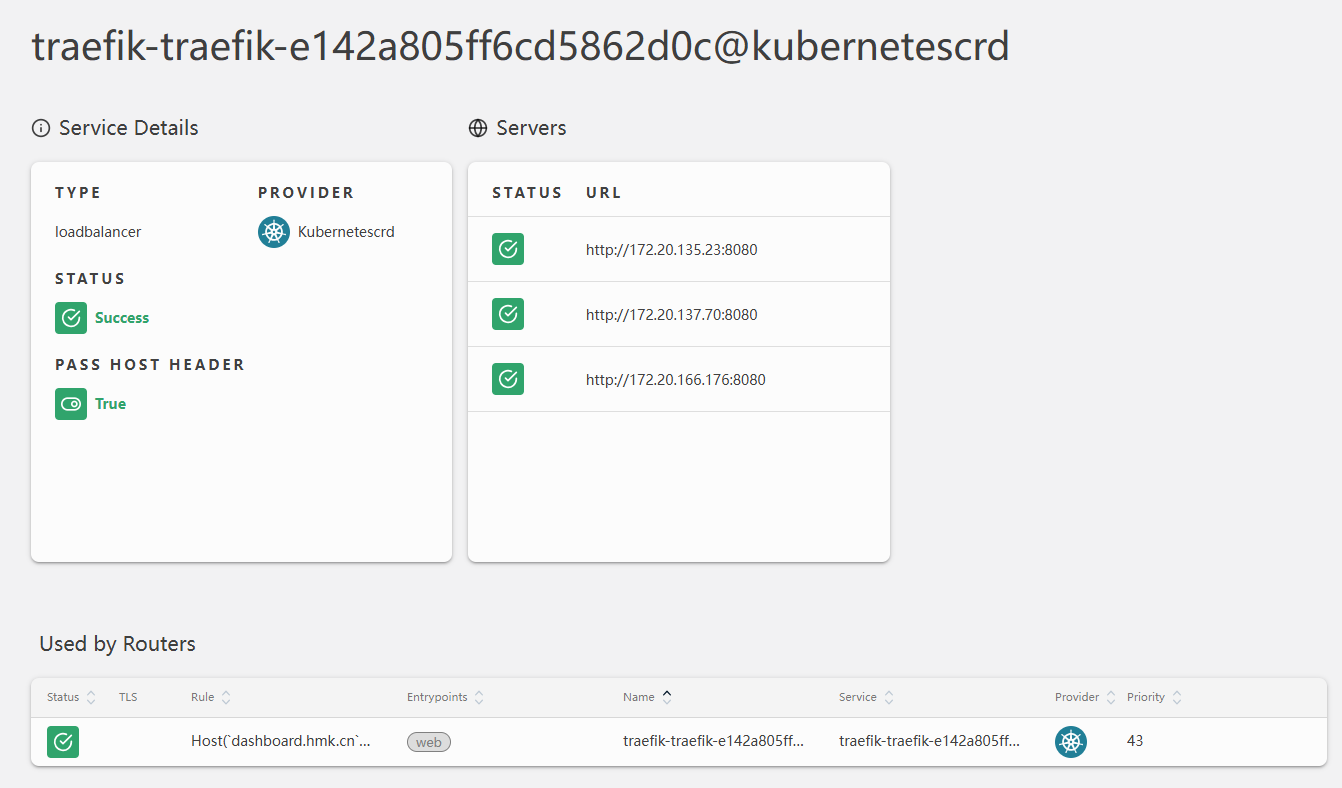
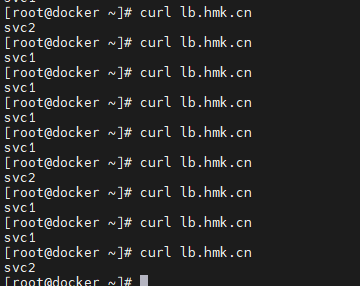
5.1 负载均衡
5.1.1 创建deployment控制器类型应用
1 | [root@master1 traefik-loadbalancer]# cat loadbalancer-deploy.yaml |
5.1.2 创建Service
1 | [root@master1 traefik-loadbalancer]# cat nginxservice.yaml |
5.1.3 创建ingressroute
1 | [root@master1 traefik-loadbalancer]# cat loadbalancer-deploy-service-ingressroute.yaml |
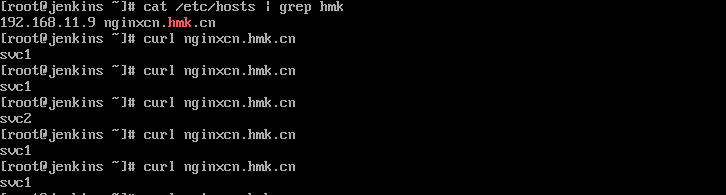
[root@docker ~]# curl lb.hmk.cn
svc2
[root@docker ~]# curl lb.hmk.cn
svc1
[root@docker ~]# curl lb.hmk.cn
svc2
[root@docker ~]# curl lb.hmk.cn
svc1
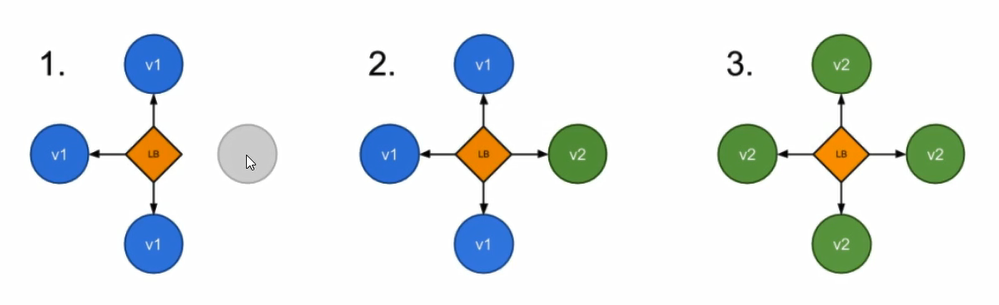
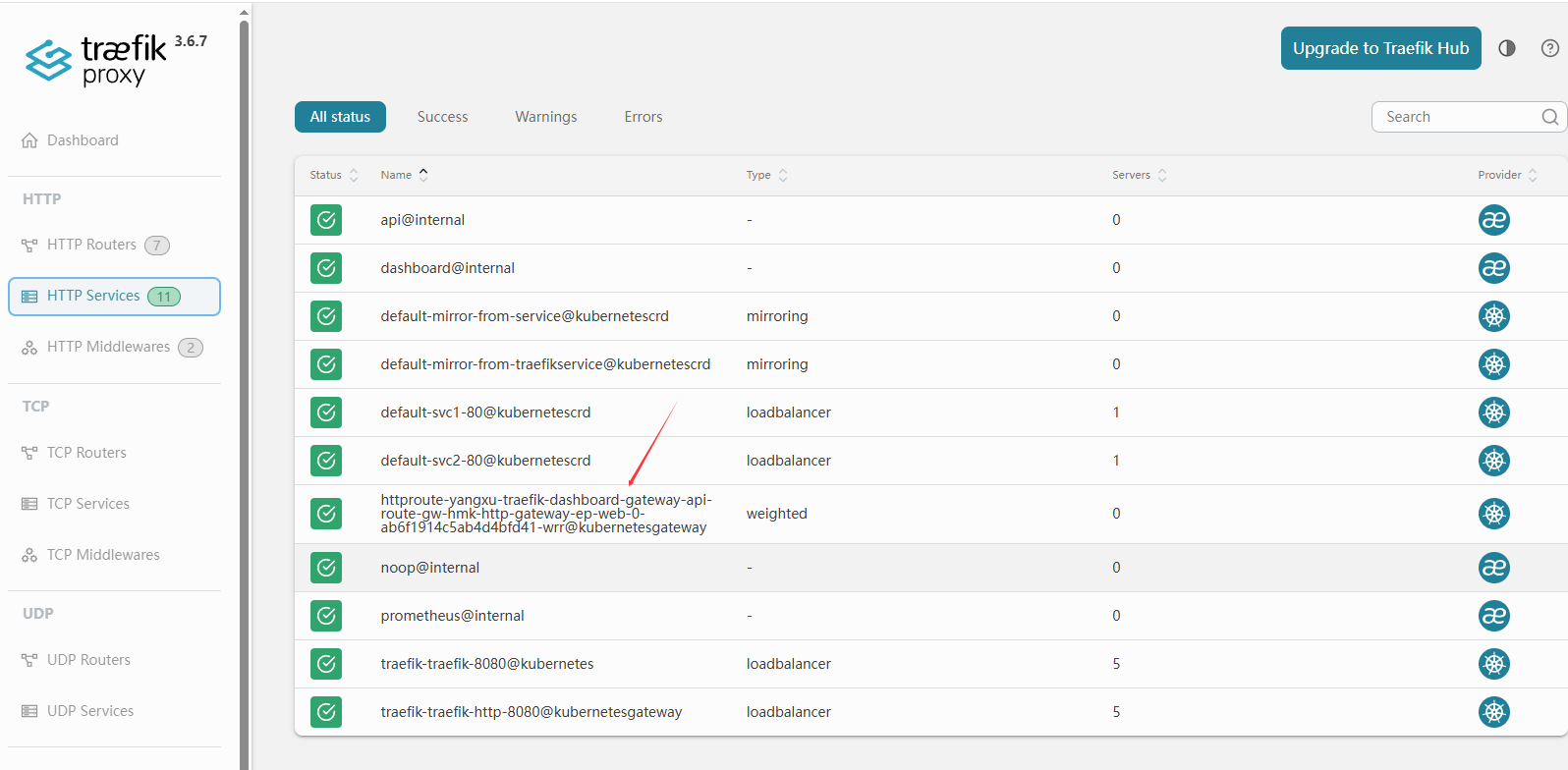
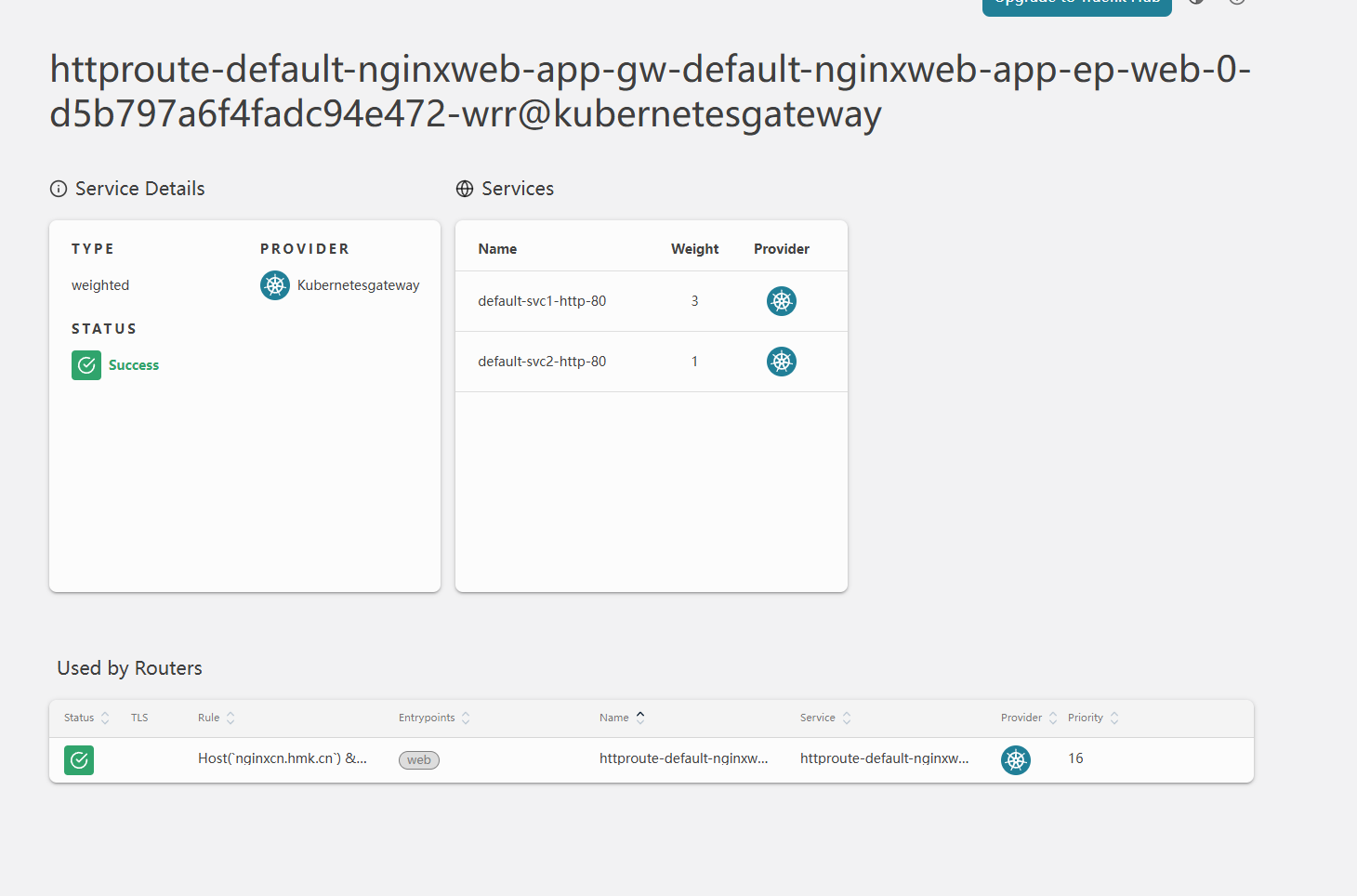
5.2 灰度发布
基于上述负载均衡案例基础之上实施。
灰度发布也成为金丝雀发布,让一部分即将上线的服务发布到线上,主要通过权重轮询的方式实现。
5.2.1 创建TraefikService
1 | [root@master1 traefik-loadbalancer]# cat traefikservice.yaml |
5.2.2 创建ingressroute
1 | [root@master1 traefik-loadbalancer]# vim traefik-wrr.yaml |
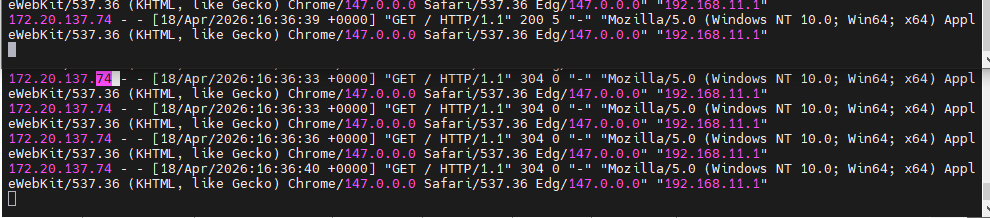
5.3 流量复制
在负载均衡的基础上实施
所谓的流量复制,也称为镜像服务是指将请求的流量复制一份发送给其他服务,并且会忽略这部分请求的响应,这个功能在做一些压测或者问题复现的时候很有用。
5.3.1 指定流量来自于kubernetes service对象
1 | [root@master1 traefik-loadbalancer]# cat mirror_from_service.yaml |
1 | [root@master1 mirror-test]# cat mirror-ingressroute.yaml |
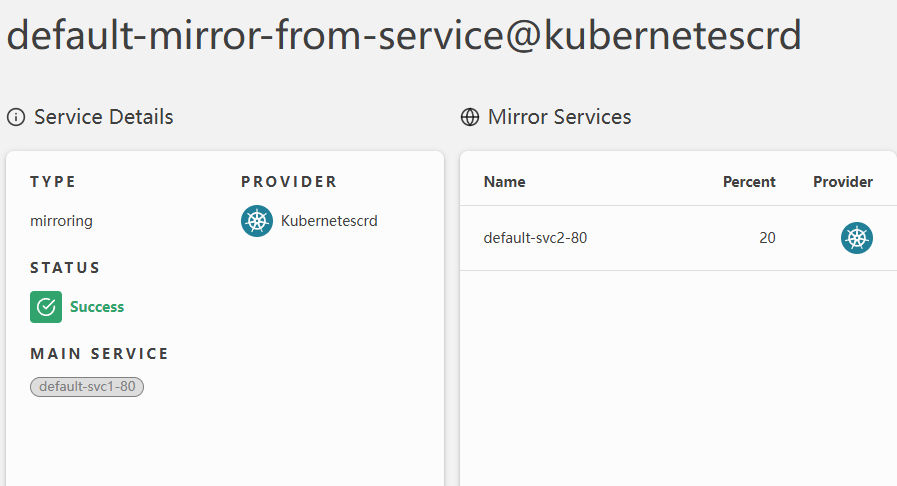
前四次流量web1 第五次web2
5.3.2 通过tarfikservice导入流量
1 | [root@master1 mirror-test]# cat mirror-from-traefikservice.yaml |
其实是加了一层 还是trafikservice -后端svc
六、Kubernetes Gateway API
6.1 Gateway API介绍
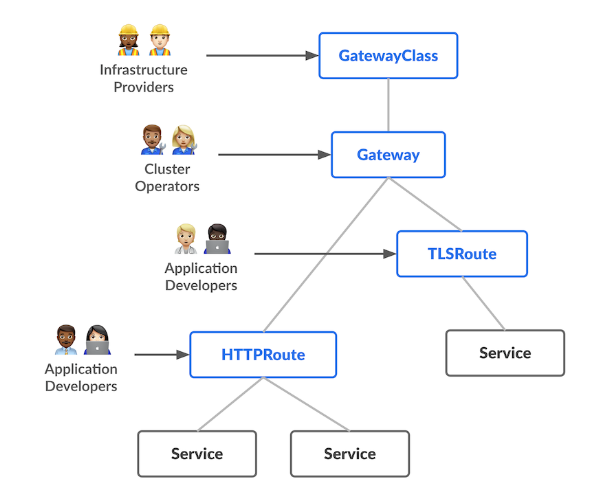
6.1.1 Gateway API 架构
Gateway APIa(之前叫Service API),是由SIG-NETWORK社区管理的开源项目,项目地址:https://gateway-api.sigs.k8s.io。主要原因是Ingress资源对象不能很好的满足网络需求,很多场景下Ingress控制器都需要通过定义annotations或者crd来进行扩展,这对于使用标准和支持是非常不利的,新推出的Gateway API 旨在通过可扩展的面向对象接口来增强服务网格。
Gateway API 是k8s中一个API资源集合,包括GatewayClass、Gateway、HTTPRoute、TCPRoute、Service等,这些资源共同为各种网络用例构建模型。
6.2kubernetes gateway CRD安装
要在Traefik 中使用Gateway API,首先我们要手动安装Gateway API的CRDs,使用如下命令安装,将安装GatewayClass、Gateway、HTTPRoute、TCPRoute、HTTPRoute、TCPRoute等CRDs:
1 | [root@master1 traefik]# kubectl apply -f "https://github.com/kubernetes-sigs/gateway-api/releases/download/v1.5.1/standard-install.yaml" |
6.3 为traefik授权(RBAC)
1 | [root@master1 gateway]# cat gateway-rbac-traefik.yaml |
可以发现traefik的log 没有gateway的warning信息了
6.4 Traefik 开启Gateway API的 Gateway api支持
providers .kubernetesGateway
启用traefik的时候默认增加了
1 | providers: |
6.5 创建Gateway API的GatewayClass
1 | [root@master1 gateway]# cat gatewayclass.yaml |
6.6 Gateway API应用案例
6.6.1 通过Gateway API 方式暴露traefik dashboard
6.6.1.1 创建gateway
1 | [root@master1 tarefik-dashboard]# cat traefik-dashboard-gateway.yaml |
互斥关系
| 场景 | 写法 |
|---|---|
| 允许所有命名空间 | from: All(不能带 selector) |
| 只允许同命名空间 | from: Same(不能带 selector) |
| 按标签选择命名空间 | from: Selector + 必须带 selector |
如果想用 selector,必须改成
1 | namespaces: |
同时要给 namespace 打标签:
1 | kubectl label namespace hmk gateway-access=true |
6.6.1.2 创建HTTPRoute
1 | [root@master1 tarefik-dashboard]# cat traefik-dashboard-httproute.yaml |
3.0+ 以后版本改动较大
6.6.1.3允许授权
1 | [root@master1 tarefik-dashboard]# cat allow-yangxu-to-tracfiksvc.yaml |
Gateway 里的 allowedRoutes
只管:
✅ 哪个命名空间的 路由 (HTTPRoute) 可以挂到我这个网关上面
ReferenceGrant
只管:
✅ 哪个命名空间的 路由 (HTTPRoute) 可以访问别的命名空间的 Service
一个管「路由能不能挂靠网关」
一个管「路由能不能跨 ns 访问后端服务」
6.6.1.4 在集群之外访问
6.6.2 通过Gateway API 方式暴露web应用
nginx-deploy
1 | [root@master1 deploy-gateway]# cat gatewayapi-web.yml |
gateway
1 | [root@master1 deploy-gateway]# cat gatewayapi-web-gateway.yml |
1 | kubectl label ns default app=nginx |
httproute
1 | [root@master1 deploy-gateway]# cat nginx-httproute.yaml |
同一个命名空间默认default的ns,所以不用授权
ReferenceGrant
6.6.3 金丝雀发布
Gateway APIs规范可以支持的另一个功能是金丝雀发布,假设你想在一个断点上运行两个不同的服务(或统一服务的不同版本),并将一部分请求路由到每个端点,则可以通过修改你的HTTPRoute实现
使用前面的nginx.yaml
1 | [root@master1 mirror-test]# cat nginx.yaml |
gateway:或者使用前面创建的gateway
如果后端service 与httproute不在一个ns,需要允许授权
1 | [root@master1 canary]# cat gateway-cn.yaml |
httproute:
1 | [root@master1 canary]# cat httproute.yaml |
test:
浏览器访问查看log效果
集群外主机测试: